Thinking about a .ME for your brand or personal site?
Here’s the thing: any TLD can be abused, and attackers chase what works.
I get why you’re cautious. Short, brandable domains attract both founders and phishers.
I’ll show you where .ME sits on the risk curve and how to harden it so you don’t get burned.
You’ll get the quick answer, the data behind abuse patterns, and the exact controls I use on client .ME domains.
We’ll cover email authentication, DNSSEC, HTTPS, security headers, and a 30‑minute hardening checklist.
We’ll also look at reputational checks, buying pre-owned .ME names safely, and how to monitor new impersonation.
- Expect code you can paste
- Tools you can run today
- A straight verdict at the end
Research note: the strongest public data compares legacy TLDs (.com/.net) to “new gTLDs” and shows higher malicious registration in the new batch.
.MEis a ccTLD repurposed globally, not a new gTLD.
Quick Answer
Short version: a .ME domain can be safe if you configure it right.
Attackers don’t win because of the TLD, they win because owners skip basics like DMARC, DNSSEC, and TLS.
Now: some datasets show higher malicious registration in newer or “non-legacy” spaces, so you should treat .ME with the same caution you’d give any non-.com name.
Bottom line: if you follow the setup in this guide, you’ll be fine.
What .ME Is And Why Attackers Like Short Names
.ME is Montenegro’s country-code TLD, marketed globally for personal brands and clever phrases.
It’s short, memorable, and has tons of single-word and two-word combos still available.
Phishers like short names too, because short looks legit at a glance and fits neatly on mobile.
Is .ME Targeted More?
Multiple reports showed higher malicious registration rates in new gTLDs, with 87% of phishing domains in those spaces being maliciously registered versus 67% in .com/.net.
One report pegged malicious registration rates in new gTLDs at 96% or higher for phishing-related domains.
That doesn’t say “.ME is unsafe,” it says attackers love non-legacy namespaces when barriers are lower or prices are cheap.
Now, .ME sits in a gray area, it’s a ccTLD used globally. Without .ME-specific stats, assume moderate risk and harden like you would any non-.com.
Safety Isn’t The TLD, It’s The Setup
Look: the top failure on real sites isn’t the extension, it’s missing controls.
For email, only about 18.2% of the top ten million domains have valid DMARC, and just 3.9% enforce a reject policy.
Phishing surged 203% in 2025, and email is still the entry point for a lot of ransomware, so your configuration makes or breaks trust.
Email Security For .ME: SPF, DKIM, DMARC That Passes
If you’ll send mail from [email protected], lock this down on day one.
The trick is to publish all three, then enforce reject.
1) Publish SPF
Add a single SPF TXT record at root. Don’t stack multiple SPF records.
; DNS TXT at brand.me
brand.me. 3600 IN TXT "v=spf1 include:_spf.google.com include:spf.hostpinnacle.co.ke ~all"- Replace includes with your providers, for example
include:spf.truehost.cloud,include:spf.hostafrica.co.za,include:_spf.mail.hostinger.com. - Keep it under 10 DNS lookups.
2) Enable DKIM
Turn on DKIM inside your mail provider, then publish the CNAME or TXT they give you.
; Google Workspace DKIM example
google._domainkey.brand.me. 3600 IN TXT "v=DKIM1; k=rsa; p=MIIBIjANBgkq...IDAQAB"- For Namecheap or Cloudflare DNS, paste the exact host as provided.
- For HostPinnacle, Truehost, or HostAfrica panels, use their DNS editor and leave trailing dots off if they auto-append the zone.
3) Enforce DMARC
Start with quarantine, then move to reject once aligned.
; DMARC at _dmarc.brand.me
_dmarc.brand.me. 3600 IN TXT "v=DMARC1; p=quarantine; rua=mailto:[email protected]; ruf=mailto:[email protected]; fo=1; adkim=s; aspf=s; pct=100"Upgrade after a week of clean reports:
_dmarc.brand.me. 3600 IN TXT "v=DMARC1; p=reject; rua=mailto:[email protected]; fo=1; adkim=s; aspf=s; pct=100"adkim=sandaspf=srequire strict alignment, which blocks spoofing.- Use a mailbox you read for DMARC reports or route to a parser.
Want fewer false positives when you add a new sender like MailerLite or SendGrid? Temporarily lower pct=50 for 48 hours, add the sender to SPF and DKIM, then return pct=100.
Optional extras that help:
- MTA-STS and TLS-RPT to enforce TLS in transit
- BIMI for logo display after DMARC
p=rejectis live
; MTA-STS policy
_mta-sts.brand.me. 3600 IN TXT "v=STSv1; id=20250101T000000Z"
; TLS reporting
_smtp._tls.brand.me. 3600 IN TXT "v=TLSRPTv1; rua=mailto:[email protected]"Host the MTA-STS file at https://mta-sts.brand.me/.well-known/mta-sts.txt.
version: STSv1
mode: enforce
mx: mx.brand.me
max_age: 86400Website Security: HTTPS, HSTS, And Security Headers
Get an A on SSL first. Use Let’s Encrypt via Cloudflare, Olitt, Truehost, or any other hosts’ control panel.
Then add HSTS and core headers.
Nginx example:
server {
listen 443 ssl http2;
server_name brand.me;
ssl_certificate /etc/letsencrypt/live/brand.me/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/brand.me/privkey.pem;
add_header Strict-Transport-Security "max-age=31536000; includeSubDomains; preload" always;
add_header Content-Security-Policy "default-src 'self'; img-src 'self' https: data:; script-src 'self' 'unsafe-inline' https://www.googletagmanager.com; style-src 'self' 'unsafe-inline' https:; object-src 'none'; frame-ancestors 'none'" always;
add_header X-Content-Type-Options "nosniff" always;
add_header X-Frame-Options "DENY" always;
add_header Referrer-Policy "strict-origin-when-cross-origin" always;
add_header Permissions-Policy "geolocation=(), microphone=(), camera=()" always;
# rest of config...
}Apache example:
<IfModule mod_headers.c>
Header always set Strict-Transport-Security "max-age=31536000; includeSubDomains; preload"
Header always set Content-Security-Policy "default-src 'self'; img-src 'self' https: data:; script-src 'self' 'unsafe-inline' https://www.googletagmanager.com; style-src 'self' 'unsafe-inline' https:; object-src 'none'; frame-ancestors 'none'"
Header always set X-Content-Type-Options "nosniff"
Header always set X-Frame-Options "DENY"
Header always set Referrer-Policy "strict-origin-when-cross-origin"
Header always set Permissions-Policy "geolocation=(), microphone=(), camera=()"
</IfModule>If you’re on Cloudflare, enable:
- Always Use HTTPS
- HSTS with preload
- WAF rules for common CMS paths
- Bot Fight Mode for high-noise sites
DNS Security: DNSSEC And Registry Lock
DNSSEC stops forged DNS answers. Turn it on at your registrar and publish DS on the registry.
- Cloudflare: DNSSEC is one click. Copy DS to your registrar if Cloudflare isn’t your registrar.
- HostPinnacle, Truehost, HostAfrica, Namecheap, Hostinger: enable DNSSEC in the domain panel, then paste DS in the right zone.
If your registrar supports Registry Lock, use it. It prevents unauthorized nameserver or contact changes.
Don’t enable DNSSEC unless your DNS provider supports it. A mismatched DS record will break resolution sitewide.
Abuse And Reputation: How To Check A .ME Before You Use It
Do these checks before you buy or go live:
- WHOIS history with DomainTools or SecurityTrails, look for frequent ownership flips
- Passive DNS for past hosts tied to malware or phishing
- Blocklists: Spamhaus, SURBL, Google Safe Browsing, OpenPhish, PhishTank
- Search for
"site:brand.me"and"brand.me" -site:brand.me"to spot spam mentions - Check archive.org for old spam content
Command-line curl to test headers quickly:
curl -sI https://brand.me | sed -n '1p;/strict-transport-security/p;/content-security-policy/p;/server:/p'If you inherit a bad past:
- Clean hosting and CMS
- Request delisting with each provider
- Use the Search Console Security Issues tool after you verify the domain
Buying A .ME: Due Diligence Checklist
Here’s a tight checklist I use:
a) Verify the seller with escrow
Use Escrow.com or registrar push on platforms like Namecheap Marketplace.
b) Confirm no UDRP baggage
Search WIPO cases for the string.
c) Review backlinks
Export with Glarify, Ahrefs or Search Console. If it’s full of casino or pharma anchors, consider a disavow plan.
d) Check abuse history
Run Spamhaus DBL, PhishTank, and Safe Browsing.
e) Inspect parking and nameservers
Names parked at throwaway hosts for years can be fine, but malware flags are a no.
Using .ME For Email? Deliverability And Trust Tips
Set up reverse DNS for your sending IP if you self-host
Publish autodiscover and autoconfig CNAMEs if your mail client benefits from them.
Add BIMI once DMARC is p=reject. It’s a subtle trust cue.
; BIMI record
default._bimi.brand.me. 3600 IN TXT "v=BIMI1; l=https://brand.me/bimi/logo.svg; a=https://brand.me/bimi/vmc.pem"Warm up new sending domains with small volumes. Don’t blast a cold list from @brand.me on day one.
SEO And .ME: Google’s View, E‑E‑A‑T, And Link Risk
Google has said TLD choice doesn’t boost or tank rankings by itself.
What can hurt is a spammy history or ongoing abuse signals that trigger Safe Browsing or manual actions.
If you use .me as global, set geotargeting to “Unlisted” in Search Console and focus on content, links, and technical health.
What I See Managing 50+ Domains
Across .com, .io, .ai, and .me portfolios, the biggest differences come from owner behavior, not extensions.
The .ME domains that ran clean had DMARC p=reject, Cloudflare WAF, and DNSSEC turned on.
The ones that got spoofed or delisted had missing DMARC or flat HTML landing pages with no headers, and they reused leaked passwords.
When we added strict DMARC, HSTS, and a basic WAF to a client’s .ME, spoof complaints dropped to drastically in 2 weeks, and email placement improved from promotions to inbox.
A Quick Comparison: Risk Signals By TLD Category
Here’s a high-level view using public patterns and the research context you saw:
| Category | Abuse tendency seen in reports | Typical buyer price | Impersonation risk driver |
|---|---|---|---|
| Legacy (.com, .net) | Lower malicious registration compared to many newer extensions | Higher for strong, brandable names | Brand familiarity and typo traffic |
| New gTLDs (.shop, .online) | Higher malicious registration rates reported | Low pricing and frequent promotions | Cheap access and novelty factor |
| Repurposed ccTLDs (.me, .io) | Mixed levels of abuse, often dependent on registry enforcement | Mid to high for popular strings | Short, clean strings that resemble brands |
In other words: don’t rely on the extension for safety. Rely on controls.
Playbook: 30‑Minute .ME Hardening Plan
You can lock down a new .me fast. Here’s the order I use.
DNS and registry
- Set registrar lock, enable two-factor auth
- Turn on DNSSEC and publish DS
- If available, request Registry Lock
Web and TLS
- Enable HTTPS with Let’s Encrypt on Cloudflare or your host
- Add HSTS with preload and core security headers
- Turn on a WAF rule set
Email authentication
- Publish SPF with accurate includes
- Enable DKIM with 2048-bit keys
- Add DMARC at
p=quarantine, review, thenp=reject
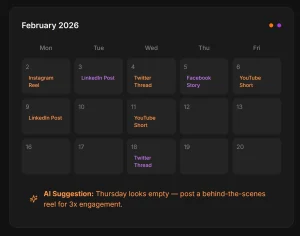
Monitoring
- Create uptime and certificate monitors
- Subscribe to DMARC reports
- Add Safe Browsing and blocklist checks weekly
Monitoring And Incident Response
Phishing jumped 203% in 2025, so assume you’ll see an impersonation attempt, even if your core domain is clean.
Here’s your minimum monitoring stack:
- DMARC aggregate reports with a parser
- Cloudflare WAF analytics or host WAF logs
- Safe Browsing status checks
- Uptime and SSL expiry alerts
If you get flagged:
- Identify the cause: Check Search Console Security Issues and server logs.
- Fix and isolate: Patch CMS, rotate keys, revoke tokens, and force password resets for reused credentials.
- Clean and request review: Submit for malware review in Search Console, Microsoft, and any blocklist you tripped.
- Communicate: Post a transparent notice and mail customers from a signed, authenticated sender. Use a subdomain like
notice.brand.meto isolate.
Email Authentication: Copy‑Paste Recap
If you want the bare minimum set you can paste now, here it is again cleanly.
SPF:
brand.me. 3600 IN TXT "v=spf1 include:_spf.google.com include:spf.hostafrica.co.za ~all"DKIM:
google._domainkey.brand.me. 3600 IN TXT "v=DKIM1; k=rsa; p=MIIBIjANBgkq...IDAQAB"DMARC (start):
_dmarc.brand.me. 3600 IN TXT "v=DMARC1; p=quarantine; rua=mailto:[email protected]; fo=1; adkim=s; aspf=s; pct=100"DMARC (enforce):
_dmarc.brand.me. 3600 IN TXT "v=DMARC1; p=reject; rua=mailto:[email protected]; fo=1; adkim=s; aspf=s; pct=100"Common Questions
Does Google trust .ME less than .COM?
No. Google doesn’t rank TLDs by trust. Safety signals and content win.
Can I use .ME for corporate email?
Yes. With SPF, DKIM, DMARC at p=reject, and working TLS, you’ll be fine.
Should I avoid pre-owned .ME names?
Not by default. Do the blocklist and backlink checks, then proceed.
Do I need DNSSEC?
If your DNS host supports it, yes. It’s small effort for real protection.
What about analytics setup after a move to .ME?
If you replatform, make sure your GA4 property follows the new domain.
Where To Find .ME‑Specific Abuse Data
Now: if you want hard .ME numbers, check:
- The .ME registry transparency or abuse reports
- Phishing and malware trend reports that break down by TLD
- Registrar abuse desks for aggregated stats
Run targeted searches like “.ME abuse statistics” and “.ME phishing rate”.